- The Good, the Bad and the Ugly in Cybersecurity – Week 17by SentinelOne (Cybersecurity Blog | SentinelOne) on April 24, 2026 at 3:48 pm
BlackCat insider faces 20 years, China-linked actors hide attacks via hijacked home routers, and ShadowBrokers leak links to pre-Stuxnet sabotage framework.
- Hypersonic Supply Chain Attacks: One Solution That Didn’t Need to Know the Payloadby Matt Berry (Cybersecurity Blog | SentinelOne) on April 22, 2026 at 4:44 pm
Learn how SentinelOne has stopped three recent zero-day supply chain attacks with AI-driven defense built for machine-speed threats.
- Automation at Machine Speed: Rethinking Execution in Modern Cybersecurityby SentinelOne (Cybersecurity Blog | SentinelOne) on April 20, 2026 at 6:43 pm
Machine-speed threats demand machine-speed defense—see how AI and automation cut dwell time and outpace attackers.
- Frontier AI Reinforces the Future of Modern Cyber Defenseby SentinelOne (Cybersecurity Blog | SentinelOne) on April 16, 2026 at 7:33 pm
As OpenAI and Anthropic advance frontier AI, SentinelOne delivers AI-native, machine-speed cyber defense at global scale.
- Securing the Software Supply Chain: How SentinelOne’s AI EDR Autonomously Blocked the CPU-Z Watering Hole Cyber Attackby SentinelOne (Cybersecurity Blog | SentinelOne) on April 14, 2026 at 10:59 pm
On April 9, 2026, cpuid.com was actively serving malware through its own official download button. Threat actors had compromised the CPUID domain at the API level and were silently redirecting legitimate download requests to attacker-controlled infrastructure. The attack ran for approximately 19 hours. Users who navigated directly to the official site received a legitimate, properly
- Edge Decay: How a Failing Perimeter Is Fueling Modern Intrusionsby SentinelOne (Cybersecurity Blog | SentinelOne) on April 9, 2026 at 1:00 pm
Edge devices are prime targets — learn how attackers exploit the perimeter to gain access, persist, and pivot to identity.
- Securing the Supply Chain: How SentinelOne®’s AI EDR Stops the Axios Attack Autonomouslyby SentinelOne (Cybersecurity Blog | SentinelOne) on April 2, 2026 at 7:50 pm
Read our blog post to learn how SentinelOne’s AI EDR autonomously stopped a global LiteLLM supply chain attack before execution.
- The Identity Paradox: The Hidden Risks in Your Valid Credentialsby SentinelOne (Cybersecurity Blog | SentinelOne) on April 2, 2026 at 1:00 pm
Identity attacks are rising as trust expands — learn how to detect misuse, close gaps, and defend beyond authentication.
- The Implementation Blind Spot | Why Organizations Are Confusing Temporary Friction with Permanent Safetyby Chris St. Myers (Cybersecurity Blog | SentinelOne) on April 1, 2026 at 1:00 pm
Our new blog post explores the ‘cognitive rust belt’ — how AI friction masks skill loss and why organizations must act now.
- How SentinelOne’s AI EDR Autonomously Discovered and Stopped Anthropic’s Claude from Executing a Zero Day Supply Chain Attack, Globallyby SentinelOne (Cybersecurity Blog | SentinelOne) on March 31, 2026 at 7:12 pm
Read our blog post to learn how SentinelOne’s AI EDR autonomously stopped a global LiteLLM supply chain attack before execution.
- Build Physical Security Superpowers with Smart Bullet Cameras and Multi-Imagersby Lesly Anzo (The Meraki Blog) on March 17, 2025 at 3:00 pm
Physical security breaches are of top concern for CSOs. Protecting your organization requires an approach as proactive and advanced as cybersecurity. But with the latest smart cameras, it doesn’t have to add complexity. The post Build Physical Security Superpowers with Smart Bullet Cameras and Multi-Imagers appeared first on The Meraki Blog.
- Cisco Meraki for Government Achieves FedRAMP® Moderate Authorizationby Lawrence Huang (The Meraki Blog) on February 25, 2025 at 1:12 pm
Cisco Meraki is excited to announce that we have achieved FedRAMP® Moderate and StateRAMP® Moderate Authorization. Built on our reliable and scalable Cisco Meraki cloud networking platform, trusted by 75% of the Fortune 500, our Cisco Meraki for Government solution addresses the unique security and cloud-first needs of government agencies. Sponsored by the Cybersecurity and Read more... The post Cisco Meraki for Government Achieves FedRAMP® Moderate Authorization appeared first on The Meraki Blog.
- Addressing Loss Prevention and Keeping Retail Customers Safeby Lesly Anzo (The Meraki Blog) on December 11, 2024 at 4:00 pm
In a pleasant retail environment, there’s likely a lot going on behind the scenes. Learn how businesses are using next-gen physical security solutions to keep guests and employees safe, protect merchandise, and fend off fraud—even during chaotic peaks of holiday shopping. The post Addressing Loss Prevention and Keeping Retail Customers Safe appeared first on The Meraki Blog.
- AI and IoT: Everything You Need to Know by Cisco Meraki (The Meraki Blog) on September 10, 2024 at 3:00 pm
Artificial intelligence and the Internet of Things are converging to revolutionize connectivity and security. Maximize their potential by taking stock of the benefits and risks that each offer. The post AI and IoT: Everything You Need to Know appeared first on The Meraki Blog.
- It’s Time to Take Control of Experiences and Transform Infrastructure Operations for AIby Jonathan Davidson (The Meraki Blog) on June 4, 2024 at 4:23 pm
Cisco Networking Cloud platform has made phenomenal progress toward continuous intelligence, predictive analytics, and automated remediation over the past 12 months. The post It’s Time to Take Control of Experiences and Transform Infrastructure Operations for AI appeared first on The Meraki Blog.
- Cisco Live 2024: Ensure Digital Resilience, Pervasive Security, and Simpler Operationsby Lawrence Huang (The Meraki Blog) on June 4, 2024 at 3:07 pm
How do you effectively manage experiences if you no longer own all the infrastructure? The answer is at the heart of new operational innovations and infrastructure announced at Cisco Live 2024. They’re all part of the Cisco Networking Cloud platform. The post Cisco Live 2024: Ensure Digital Resilience, Pervasive Security, and Simpler Operations appeared first on The Meraki Blog.
- Simplify 5G Fixed Wireless Access and Scale Secure Connectivity to More Placesby Pratik Desai (The Meraki Blog) on May 29, 2024 at 7:03 am
Cisco introduces its first 5G Standalone (SA) fixed wireless access devices, the Meraki MG52 and MG52E. Powered by the Cisco secure networking platform, these devices help businesses scale robust, always-on, 5G-connected experiences to more people and places — without compromising scale and performance. The post Simplify 5G Fixed Wireless Access and Scale Secure Connectivity to More Places appeared first on The Meraki Blog.
- Systems Manager Scores Nod of Approvalby George Mokdessi (The Meraki Blog) on April 5, 2024 at 3:00 pm
Device management magic from Meraki earns Android Silver Partner status The post Systems Manager Scores Nod of Approval appeared first on The Meraki Blog.
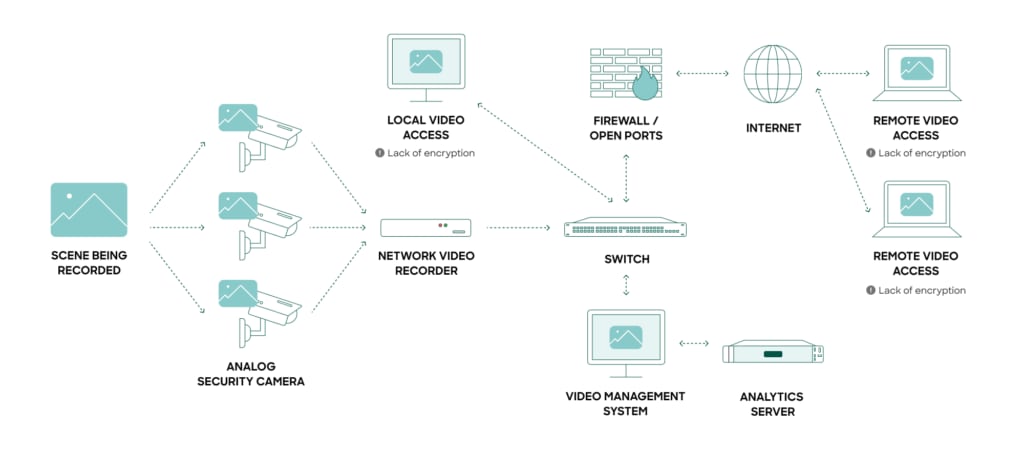
- Do More With Less Using Cloud-Based Securityby Mike Maxsenti (The Meraki Blog) on March 18, 2024 at 3:55 pm
How a single view of security is changing video security and access control The post Do More With Less Using Cloud-Based Security appeared first on The Meraki Blog.
- Is Your Network Infrastructure Ready for More IoT Devices?by Minyi Pan (The Meraki Blog) on February 13, 2024 at 8:00 am
Stay ahead of challenges with new Catalyst 9300-M models The post Is Your Network Infrastructure Ready for More IoT Devices? appeared first on The Meraki Blog.